Picture this: Last December, an accounts payable clerk is drowning in year-end chaos. Her phone buzzes. It’s her CEO. Well, it looks like her CEO.
“Need $3,000 in Apple gift cards for clients. Urgent. Scratch the backs, email me the codes.”
Weird? Sure. But it’s the holidays. Everything’s weird and rushed. The text shows his name. She buys the cards, sends the codes, and boom—money’s gone. Scammer disappears. Company eats the loss.
Three thousand bucks hurts, but you survive that.
Now let me tell you about the company that didn’t.
That same month, Orion S.A., a Luxembourg chemical manufacturer, got hit with what looked like normal business emails. Wire transfer requests. Nothing flashy. Just everyday stuff from people they work with all the time. The emails looked legit. They felt urgent but not suspiciously urgent. The kind of thing you process and move on.
Someone hit send on those transfers.
$60 million vanished. More than half their annual profits, straight into criminal accounts.
And here’s the thing—one phone call could’ve stopped it. Just one “hey, did you actually send this?” conversation.
Look, I know what you’re thinking. “We’re too small for that.” Or “we’re pretty careful, we’d catch something.”
Here’s what actually happened in 2023: Gift card scams alone? $217 million in losses. Business email compromise attacks? They made up 73% of cyber incidents in 2024. And the holidays? That’s when criminals go into overdrive because your team is already running on fumes, processing more transactions than usual, and juggling family stuff on top of work.
At Blue Cotton Tech Services, we watch this play out every December. It’s not about if someone’s going to try to scam your business. It’s whether your team knows what to look for when it happens.
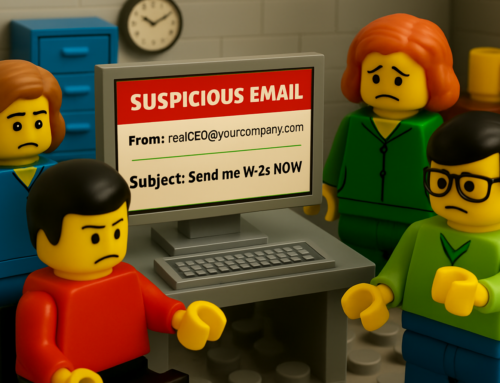
5 Scams That’ll Ruin Your Holidays (If You Let Them)
- The “Boss Needs Gift Cards” Text
Remember our accounts payable clerk? That’s the template. Someone pretending to be an executive texts or emails staff asking for gift cards—”for clients,” “for a promotion,” whatever sounds plausible. In early 2024, almost 38% of business email compromise cases involved gift cards.
Here’s how you shut it down: Make it policy—in writing—that gift cards are NEVER approved via text or email. Period. And require two different people to sign off on any gift card purchase. Train your team that if someone’s asking for gift cards electronically, especially urgently, that’s not your boss. That’s a scammer.
- The Payment Switch
This one’s sneaky. Criminals either hijack a real vendor email thread or send you “updated banking info” right when you’re paying year-end invoices. Arlington, Massachusetts lost almost $500,000 in June 2024 because they paid an invoice to “vendor” bank details that had been quietly changed by attackers.
The fix is simple but you have to actually do it: Pick a dollar amount—say $5,000 or $10,000—and make it a rule that ANY banking change above that threshold gets a phone call. Not to the number in the email. To the number you already have on file for that vendor. And require two people to approve new payment details.
- Fake Shipping Notifications
You know those “Track your package” texts or emails from UPS, FedEx, USPS? Scammers send fake versions that either steal your login credentials or drop malware on your device when you click.
The defense: Train your team to type the carrier’s website directly into the browser instead of clicking links. Bookmark your official tracking pages. Use email security tools that can flag suspicious links before they become a problem.
- The “Holiday Party” Attachment
Emails with attachments named things like “Holiday_Schedule.pdf” or “Year_End_Bonus_Info.docx” that secretly install ransomware or keyloggers when you open them.
Block macros by default on all company computers. Use email filters that actually scan attachments before they hit inboxes. And make it normal for people to verify unexpected files even if they look like they’re from HR or leadership. Better to ask and look paranoid than to click and get infected.
- Fake Charity Campaigns
Bogus charity sites, fake “company match” programs, spoofed donation pages designed to steal credit card numbers and login credentials.
Publish an approved charity list with official donation links. Make sure any “company match” program runs through your actual internal system, not some random link in an email. Teach your team to check for HTTPS, correct URLs, and real branding before they donate anything.
Why This Stuff Still Works (And How to Stop Them)
These aren’t the old Nigerian prince emails written in broken English. Modern scammers do their homework. They research your company, study your executives’ social media, use domains that look almost identical to yours, and copy language straight from your own website and emails.
All the tools that make your business run smoothly—email, online payments, cloud apps—are exactly what attackers exploit.
But here’s the good news: Companies that run regular phishing simulations cut their risk by around 60%. Multifactor authentication blocks about 99% of automated login attempts.
Yet somehow, tons of small and mid-sized businesses still rely on one-time training during orientation, passwords alone, and this vague sense that “we’re careful enough.”
That confidence? That’s exactly what scammers are banking on.
Your Holiday Defense Checklist
The Two-Person Rule
Pick a threshold—$5,000, $10,000, whatever makes sense for your business. Any transaction over that amount needs a second approver AND verbal confirmation through a different channel. Phone call, video chat, whatever. Just not the same email thread.
The Gift Card Policy
Write it down: “Gift cards will never be requested or approved by email or text.” Make it official. All gift card purchases require documented approval through your actual system.
The Vendor Verification Process
Any banking or payment change gets confirmed by phone using the number you already have on file. Log who called, when, and what they confirmed.
Turn On Multifactor Authentication
Email, banking, remote access, all your important cloud apps. Use app-based authenticators instead of SMS when you can.
The 20-Minute Briefing
Walk your team through these five scam types with real examples. Show them actual screenshots so they recognize the patterns. And make it clear: asking questions is good, not suspicious. Nobody gets in trouble for being careful.
Blue Cotton Tech Services can help you implement all this—not as a one-time checklist you forget about, but as part of an ongoing security program that actually works.
It’s Not Just About The Money
Yeah, Orion’s $60 million loss made headlines. What doesn’t make headlines are the hundreds of smaller businesses that get hit with $50,000 or $100,000 losses and never fully recover.
After a successful scam, you’re dealing with operations shutting down right when you need them most. Weeks of lost productivity while everyone’s scrambling through forensics and insurance claims. Damaged client relationships if data gets exposed. Higher insurance premiums going forward. Staff burning out. Leadership distracted from actually running the business.
The average business email compromise loss is $129,000. For a lot of small and mid-sized companies, that’s enough to derail your entire growth plan—or worse.
Keep Your Holidays Merry, Not Messy
The holidays should be about closing the year strong, rewarding your team, and serving your customers. Not cleaning up from wire fraud.
One employee at Orion could’ve stopped a $60 million loss with a single phone call.
So here’s the question: Would your team know when to stop and make that call?
Blue Cotton Tech Services helps businesses tighten up email and payment workflows, train employees to spot actual scams, put simple policies in place, and add protection layers that don’t slow everything down.
Let’s Figure Out Where You’re Exposed
If you’re not 100% confident your team could spot and stop these scams, the next step is straightforward:
Schedule a free security assessment with us.
We’ll review how money and sensitive data move through your business, identify the gaps attackers would exploit, and give you a prioritized action plan in plain English—not jargon and scare tactics.
Protect your year-end revenue and your reputation.
Schedule Your Free Security Assessment with Blue Cotton Tech Services
Because the best thing you can do for your business this holiday season is give it something scammers can’t touch: peace of mind.